Iocane Security Practice – Overview
Information security has moved from a stand-alone silo consideration to an all-encompassing issue which impacts every level of business. It no longer works as an afterthought.
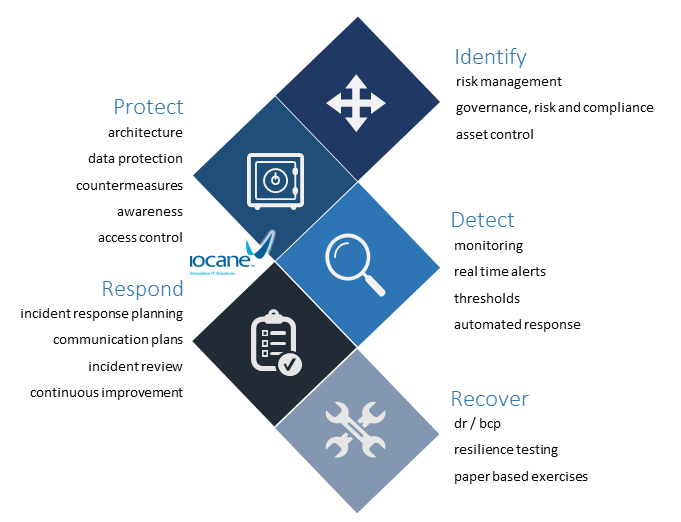
5 Tenets
The Iocane security approach aligns to 5 key tenets:
identify threats, protect the assets, detect problems, respond appropriately and recover swiftly
Simplified Security
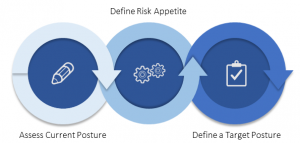
The simplified security model challenges a business to:
- Define a current state
- Decide what kind of risk is acceptable
- Decide what level of control is appropriate
So what is Appropriate?
The simplified security model sees the term appropriate as mapped directly to a business need or outcome. In other words, wrapping a security control, solution or process around a particular asset because you should, not because you can
Knowing when you should do something only comes with traceability, and traceability only comes as a by-product of architecture
What kind of architecture?
The term architecture can mean many things to many people, the Iocane security reference model is driven by the SABSA® framework which asks:
What are you trying to do?
When are you doing it?
Where are you doing it?
Who is involved?
How are you trying to do it?
Why are you doing it?
Security Service Offerings
Iocane offers several levels of professional security services including:
- Consulting and Architecture
- Policy Development
- Incident Response Planning
- Risk Assessment Services
- Engineering Services
- High Level Logical Design
- Low Level Logical Design
- Fault and Root Cause Analysis
- Ad-Hoc Security Engineering
- Security Managed Services
- 24/7 Monitoring
What our customers say:
“I wanted to drop you a quick email to say that we are 75% through SOA2 for IRAP. The assessor has informed us that we are the best shape of all the assessments he has done thus far and was very impressed at the level of detail we have prepared. We have one last session to go before submission. On the back of this we are submitting tenders for business in other parts of the state. We have a bit of work to do for SOA 3 but I feel confident we will achieve this.
I wanted to personally thank you for all of your efforts in working with us on this piece. We were somewhat in the dark about where to start and you provided us with clarity and confidence. Often in this space we hear what isn’t going well and what we can do better. We don’t take the time to reflect on what we have achieved and look back on how far we have come! Looking forward to working with you again.”
More Information
Download the Iocane security practice overview 1 pager: Iocane Security BrochureV3
Keep up with the latest in security related content at the Iocane Security Blog
The ASD essential 8